OURDIFFERENCE
OURDIFFERENCE
* Texas A&M Commerce does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from Texas A&M Commerce.
OURPARTNERSHIP
The RELLIS Cybersecurity and Emerging Technologies Academy is a partnership between The Texas A&M University System (TAMUS), Texas A&M University – Commerce and the Institute for Cyber Threat Defense (ICTD). This unique collaboration is designed to provide skills development, workforce placement, and mentoring programs in the areas of cybersecurity, artificial intelligence (AI), machine learning (ML), and emerging technologies.
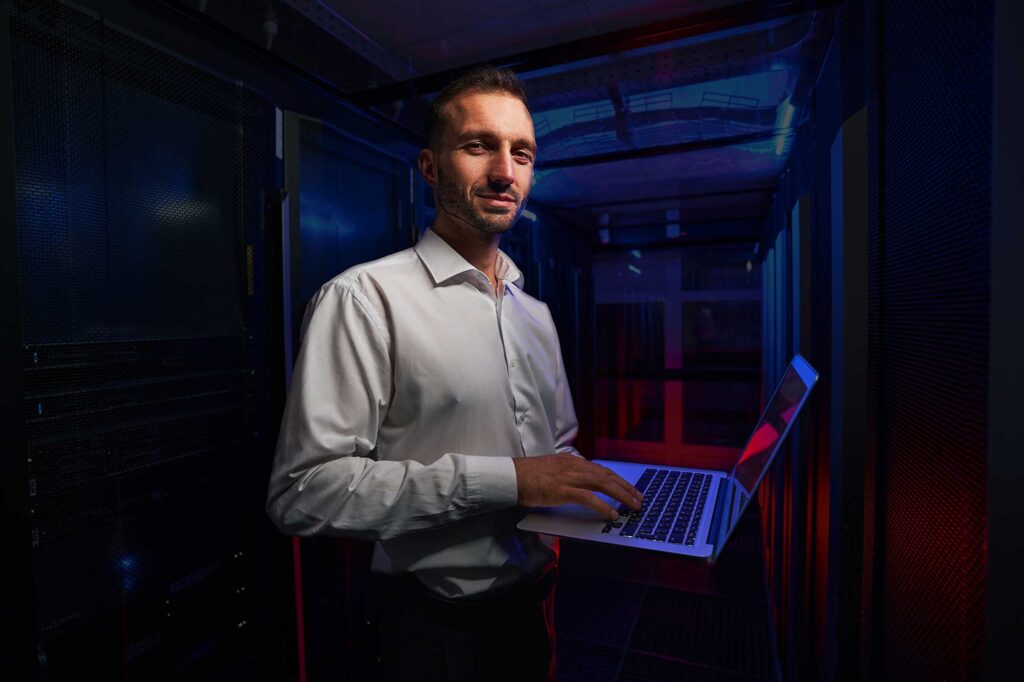
WHAT TO KNOW ABOUT ACYBER ANALYST CAREER
Why work as a Cyber Analyst?
Cyber Analysis is a popular and rewarding field where you protect businesses, organizations, and people from online threats. It involves keeping sensitive information safe, defending against cyber-attacks, and stopping hackers from causing financial harm.
What is a Cyber Analyst?
Cyber Analysis revolves around safeguarding computers, networks, and vital information from unauthorized access. This field employs various methods and tools to detect and prevent online hazards such as viruses, scams, data leaks, and other types of cybercrimes. Its core focus is on ensuring the digital world remains secure and protected.
Where can Cyber Analysts work?
Professionals in cyber analytics have diverse job opportunities across various sectors, including government agencies, companies, banks, hospitals, and schools. Additionally, they have the flexibility to work independently as consultants or freelancers, assisting different clients on specific projects. This field offers a wide range of employment options and the potential for self-employment, allowing individuals to apply their expertise in diverse settings.
What skills do you need to work in Cyber Analytics?
To be skilled in Cyber Security, you need to know a lot about computer science, technology, and programming languages. It’s also important to be good at problem-solving, paying close attention to details, and thinking carefully even in tough situations.
Do you need certifications to become a Cyber Analyst?
While certifications are not always mandatory, obtaining them can enhance your job prospects and demonstrate your expertise in Cyber Analysis. Some highly sought-after certifications include CompTIA Security+, Certified Information Systems Security Professional (CISSP), and Certified Ethical Hacker (CEH). These credentials showcase your knowledge and proficiency in relevant areas of Cyber Analysis, making you a more attractive candidate to potential employers.
Do you need training to become a Cyber Analyst?
While self-learning is possible to acquire some skills, formal education or certification in Cyber Analysis can provide you with comprehensive knowledge and expertise to excel in the field, setting you apart in the market. Enrolling in a Cyber Analysis program or obtaining certifications offers valuable real-world experience and opportunities to network with key professionals in the industry. These educational paths can significantly boost your capabilities and enhance your career prospects in the world of Cyber Analysis.
Texas A&M Commerce does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from Texas A&M Commerce. It is not required to attend Texas A&M Commerce to attain a job or earn a certain salary in a field of employment. Past students’ outcomes, starting salaries, or job prospects are not indicative of those for future and current students.
HAVE MORE QUESTIONS?ASK US
CAREER TRAINING.FOR YOUR FUTURE.
CYBERSECURITY AT A GLANCE
Cybersecurity analysts are essential to safeguarding the IT infrastructure of many companies. As the first line of defense for their companies, cybersecurity analysts manage cyber attacks to protect valuable information. Because cybersecurity is an essential role, cybersecurity related jobs are always in-demand.
OURCURRICULUM
The one-year Cyber Analyst Training Program offers a 33-week curriculum designed by the Cybersecurity and Emerging Technologies Academy. The program is 100% online and covers more content than boot camps typically offer for industry certifications. Additionally, the curriculum is employer-tailored, ensuring that it is up-to-date and advantageous to those looking to start a career in cybersecurity.
HERE'S EXACTLY WHAT YOU GET AS ACYBER ANALYST TRAINEE
CERTIFICATIONS

QuickBooks Certified User – Online

Entrepreneurship and Small Business

Microsoft Excel

Microsoft Outlook

Microsoft Office Specialist: Word
SKILLS

Security Foundations

Networking Foundations

System Administration

Network Defense
Cryptography and Access Management
Logging and Monitoring

Programming Foundations

Web Application and Project Management

Threats and Vulnerabilities

Group Project

Application Presentation and Sharing
WHAT CERTIFICATES DO WE OFFER?
CYBER SECURITY CERTIFICATES
FOR THE FIRST LINE OF DEFENSE
CERTIFICATIONS
Cyber Analyst
Certificate Awarding Institution:
Texas A&M University – Commerce
Included Certification:
CompTIA Security +
Relevant NIST NICE Specialty Areas:
Cybersecurity Defense Analysis (CDA) Cybersecurity Defense Infrastructure Support (INF) Incident Response (CIR) Vulnerability Assessment and Management (VAM)
Technologies you’ll learn:
• Monitoring/Logging
• Network Appliances
• Network Defense
• Security Threats Identification
• Virtual Machines
• Agile Project Management Methodologies
• Basic Cryptography
• Coding
Course Descriptions
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: None
The Security Foundations course will help students gain a fundamental understanding of security concepts that will be used throughout the Cyber Security track. Topics covered include basic security concepts, threat actors and attributes, organizational security, policy, procedures and frameworks, security controls business impact analysis, risk management, incident response and disaster recovery.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: None
The course will provide instruction in technical skills required in network administration and support. This course will include information on media, topologies, protocols and standards, network support, and the knowledge and skills to sit for network certification.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: None
The course will cover System Administration basics and will also provide a security orientated perspective. This course will include general system administration information on installing and configuring network component, OS familiarity and some scripting. Additional topics include threats, vulnerabilities, secure protocols, and secure system design.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: CSO100, CSO101
The Network Defense course will give students an overview of the various hardware and software tools available to defend a network against attack. Students will use various tools to assess the security posture of an organization and understand the possible impact of various vulnerabilities. Additionally, this course will cover the concepts of penetration testing and vulnerabilities testing.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: None
The course will cover the different methodologies and concepts of Cryptography and Access management. Students will be exposed to different cryptography algorithms used to ensure safe transmission, storage, and use of sensitive data. Students will also learn how to implement various access management controls and account management practices.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: CSO102
The course will give students the knowledge and skills needed to properly analyze and interpret various security related logs produced by different security related technologies. This will focus on standard logs and Intrusion Detection and Prevention Systems. Students will also gain a basic understanding of forensics analyze and presented with such related topics as chain of authority.
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: None
This course will give students programming foundations in languages utilized in the industry. This course also provides a secure foundation upon which students can build on as they progress through the program.
This learning unit is structured to allow students to practice and enhance their skills. Activities may include performing customer procedures in the salon clinic, attending field trips, participating in guest speaker lectures, practicing, remediating, and passing skills assessments, practicing skills and procedures in the lab.
Hours: Theory 9 / Laboratory 66 / Total 75 / Quarter Credits 0 / Outside Hours 0 / Prerequisites: Junior Stylist
Hours: Theory 30 / Laboratory 30 / Total 60 / Quarter Credits 4.5 / Outside Hours 15 / Prerequisites: CSO100, CSO101
The Threats and Vulnerabilities course will provide students with an in depth look at the various threats and vulnerabilities faced by every organization and technology user. These will cover those related to hardware, software, and people, including a detailed review of Social Engineering as used by various threat actors. Students will be able to identify, compare several types of attacks and related impacts.
Hours: Theory 50 / Laboratory 110 / Total 160 / Quarter Credits 10.5 / Outside Hours 15 / Prerequisites: Final Mod
The Group Project course combines each part of the program into a group project for the student. Each student will work together as a team member for the group project, which includes daily scrum meetings to cover tasks and progress while working separately to complete them. The final group project is due at the end of the course.
CAREER TRAINING.YOU CAN TRUST
ACCREDITED
Southern Careers Institute is Accredited by the Council on Occupational Education.
APPROVED
Southern Careers Institute is Approved for training by The Texas Workforce Commission.
OUR GRADUATES HAVE BEENHIRED BY



Employers are not incentivized by Southern Careers Institute (SCI) to hire our graduates. Employers are not incentivized to review or comment on the performance and outcomes of our graduates, or on SCI. Past students’ outcomes, starting salaries, and job prospects are not indicative of those for current and future students. SCI does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from SCI.
THE NUMBERSSAY IT ALL
Southern Careers Institute (SCI) does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from SCI. It is not required to attend SCI to attain a job or earn a certain salary in a field of employment. Past students’ outcomes, starting salaries, or job prospects are not indicative of those for future and current students.
As an accredited post-secondary institution, SCI has various federal financial assistance programs available for qualified students enrolled in SCI programs. This does not apply to seminar students. Financial aid is available for those who qualify.
Past students’ outcomes, starting salaries, or job prospects are not indictive of the possible job outcomes for future and current students. SCI does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from SCI.
GET UP TO $4,500FOR YOUR FUTURE
Get up to $4500 in grants toward your career training at Southern Careers Institute.
As an accredited post-secondary institution, SCI has various federal financial assistance programs available for qualified students enrolled in SCI programs. This does not apply to seminar students. Financial aid is available for those who qualify.
HEAR FROM STUDENTSJUST LIKE YOU
Past students’ outcomes, starting salaries, or job prospects are not indictive of the possible job outcomes for future and current students. SCI does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from SCI.
KICKSTART YOUR CAREER.
We pay for your certification within 3 months of graduating.
1. Pick your certification
2. Take the certification exam within 3 months of graduation
3. We will pay for it!
FACT: TODAY'S EMPLOYERSNEED YOUR SKILLS
Information Security Analysts
Occupation Code:15-1212
| Location | Mean Annual Wage |
|---|---|
| Austin | $94,490 |
| Brownsville-Harligen | $68,410 |
| Corpus Christi | $89,960 |
| Pharr | $78,360 |
| San Antonio North & South | $100,640 |
| Waco | $81,290 |
Southern Careers Institute (SCI) does not guarantee employment or a starting salary upon graduation, completion, or withdrawal from SCI. It is not required to attend SCI to attain a job or earn a certain salary in a field of employment. Past students’ outcomes, starting salaries, or job prospects are not indicative of those for future and current students.
Displayed salaries and job outlook data do not reflect the prospects of Southern Careers Institute graduates’ job placement outcomes and starting salaries. U.S. Bureau of Labor Statistics employment data, job prospects, and salary data sourced for (insert specific metro and job page) does not reflect data applicable to entry-level positions.
FINANCIAL ASSISTANCE. THE SIMPLE WAY.
Tuition Payment Plans
Workforce Funding
Private Student Loans
WHY THE RELLIS ACADEMIC ALLIANCE CYBERSECURITY AND EMERGING TECHNOLOGIES ACADEMY?
The Texas A&M University System (TAMUS) is one of the largest systems of higher education in the nation, and TAMUS’ RELLIS Academic Alliance brings students, faculty and researchers together in a unique community that encourages the pollination of ideas across people, disciplines and industries. Our network and capabilities make recruiting and workforce placement a strength for candidates looking to join our programs. Through the ICTD and TAMUS partnership, students will gain both the knowledge and experience to confidently enter the workforce.
FREQUENTLY ASKEDQUESTIONS
That’s okay! At Texas A&M Commerce, we have had a plethora of students successfully complete their programs after being away from school for long periods of time. We’re ready to meet you where you’re at, providing a community-based learning environment where you’ll feel right at home as you readjust to life as a student!
Texas A&M Commerce provides you with the training you need to sit for certifications in your chosen field. Whether it’s our Medical Assistant training program, Medical Billing and coding Specialist program, Pharmacy Technician program, Business Accounting Specialist program, HVAC program, or any other educational program available, rest assured that you will graduate ready to tackle industry-specific certifications.
We have experienced student success coordinators ready to help you with all your needs. They will assist you in building a tuition plan that is affordable for you.